Bringing Clarity to Cybersecurity
Frameworks
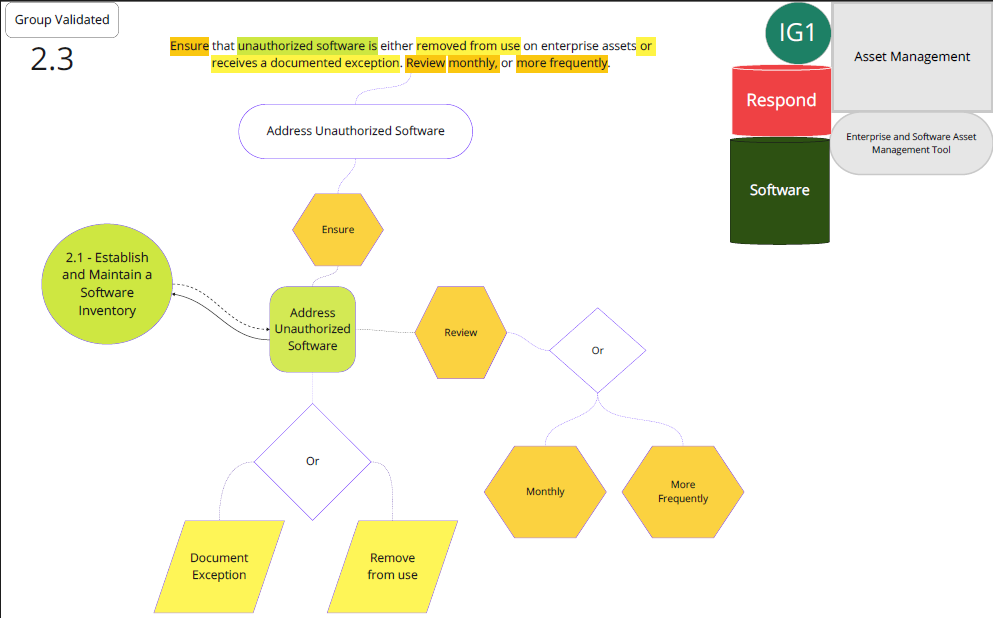
Cybersecurity frameworks tell you what to do. They don't tell you how. Framework Maps breaks each control into its core requirement, supporting elements, and implementation steps — then maps them to the tools you already use. Currently available: CIS Controls v8.1 — all 153 safeguards fully mapped.